


Home
The Decision to Commit Crime: Rational or Nonrational? – Criminology, Criminal Justice, Law & Society
Rational choice theory has received a fair amount of attention from criminal justice scholars and societal policy makers looking for an alternative to traditional deterministic theories of criminal behavior and is a core feature of several major criminological theories. In an effort to provide a more comprehensive perspective on criminal decision-making, the current paper highlights the role of emotion in the choice process and reviews factors that increase the likelihood of antisocial outcomes. The result is a theory of decision-making in which the individual is believed to act on the hedonistic and moral emotions that guide moral decision-making and where irrelevant emotions are enhanced and relevant emotions dampened by cognitive and situational factors that, in the end, serve as the foundation for criminal choice.
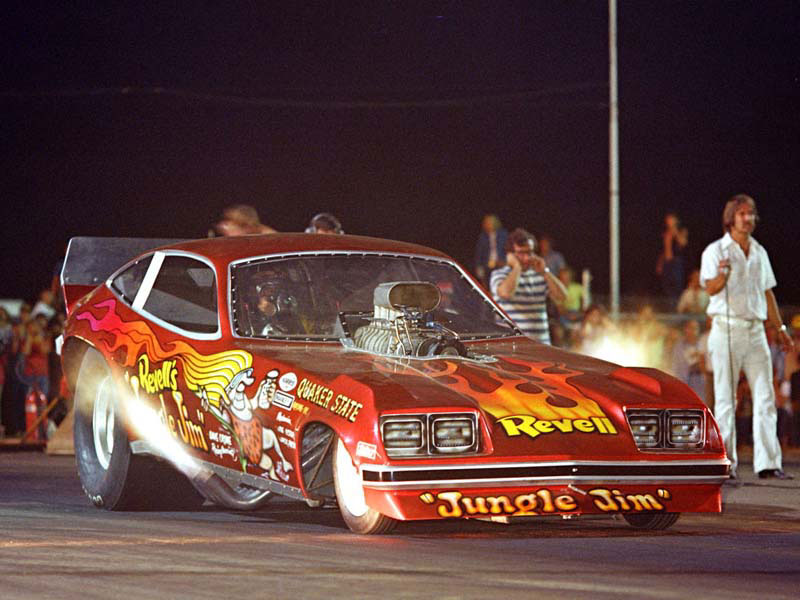
Motion Blur Removal And Its Application To Vehicle Speed Detection
ABSTRACT
Motion blur is the result when the camera shutter remains open for an extended period of time and a relative motion between camera and object occurs. Most research on this type of image degradation is focused on motion blur removal. In this work, we propose a novel approach for vehicle speed detection based on motion blurred images. The motion blur parameters are first estimated from the acquired images and then used to detect the speed of the moving object in the scene. We have established a link between the motion blur information of a 2D image and the speed information of a moving object. Experimental results are presented for both indoor environments and outdoor vehicle speed detection.
1. INTRODUCTION
Motion blur is the result when a camera shutter remains open for an extended period of time and the relative motion between the camera and the moving object that has occurred over this interval is visible in a single snapshot. Image distortions caused by motion blur can be classified as either spatially invariant (SI) or spatially
Sexual Hookup Culture: A Review
“Hookups,” or uncommitted sexual encounters, are becoming progressively more engrained in popular
culture, reflecting both evolved sexual predilections and changing social and sexual scripts. Hook-up activities may include a wide range of sexual behaviors, such as kissing, oral sex, and penetrative intercourse. However, these encounters often transpire without any promise of, or desire for, a more traditional romantic relationship.
A review of the literature suggests that these encounters are becoming increasingly normative among
adolescents and young adults in North America, representing a marked shift in openness and acceptance of uncommitted sex. We reviewed the current literature on sexual hookups and considered the multiple forces influencing hookup culture, using examples from popular culture to place hooking up in context. We argue that contemporary hookup culture is best understood as the convergence of evolutionary and social forces during the developmental period of emerging adulthood.
The Management Of Visibility | Media Coverage Of Kidnapping And Captivity Cases Around The World
Abstract
Media, Culture & Society
35(7) 791 –808
© The Author(s) 2013
Reprints and permissions:
sagepub.co.uk/journalsPermissions.navDOI: 10.1177/0163443713495075
mcs.sagepub.com
This article examines the journalistic practices associated with the management of visibility of kidnapping and captivity stories, based on a comparative study of the media coverage of seven cases of Colombian, French, Israeli, and US citizens who were taken captive in the first decade of the 21st century. Differences in the general level of visibility given to these stories are identified and explained, followed by an analysis of three patterns of high visibility management across time, termed ‘sustained visibility’, ‘delayed visibility’ and ‘cyclical visibility’. Emerging from the analysis is the complex interplay between hyper-visibility and invisibility in journalistic practices, as well as the notion of “elastic newsworthiness”, according to which news criteria are not only shaping patterns of visibility but are also being shaped by them.
The Perspectives of Academicians on Academic Jealousy
Introduction
There are emotions and actions that have been going on since the first day of humanity. One of them is undoubtedly jealousy. Although jealousy is perceived as distrust and a psychological disorder, evolutionary psychologists have suggested that jealousy has a structure obtained over time and preserves love (Demirtas, 2002). According to the Turkish Language Association (TDK, 2011), jealousy is defined as a “negative attitude when someone shows superiority or thought that a loved one is interested in someone else, envy, annoyance.”
The terms “jealousy” and “envy” in Turkish are generally thought to have the same meaning. However, these two concepts are used for different purposes. According to the Turkish Language Association (2011), envy is more often used and expressed as not standing. Envy is mostly defined as the desire for something in the hands of another individual but not in the person’s hands and the deprivation of the person who has that thing. Jealousy is expressed as the fear of losing something that exists (Özdemir, 2018).
Factors Associated With Stalking Victimization
This study examined victim characteristics as predictors of stalking victimization. Female college students (N=217) completed scales assessing the following constructs: stalking victimization, alexithymia, alcohol abuse, assertiveness, hyperfemininity, agreeableness, and dependent personality disorder. The results revealed significant negative correlations between stalking victimization and both alexithymia and agreeableness. There were significant positive correlations between stalking victimization with drinking problems and hyperfemininity. Agreeableness was found to contribute a unique portion of variance above alexithymia and drinking problems.
INTRODUCTION
Stalking has several negative ramifications for its victims. For instance, nearly half of identified stalking victims in a study conducted by Amar (2006) reported significant changes in their behaviors and routines in response to being stalked. Of these same identified stalking victims, 13 percent reported being physically abused by their stalker (Amar, 2006). A study conducted by Blackburn (1999) paints a similar, but more devastating, picture of the aftermath of stalking. In this study, it was found that 46 percent of identified stalking victims were threatened by their stalker, and of these threats, 22.8 percent of them were acted upon (Blackburn, 1999).
Broadcast Newsroom Hiring and CareerPreparation
Internships have become an integral part of many journalism and broadcasting curricula. More than 95 percent of journalism and broadcasting programs report that internships are a part of their curricula (Becker. 1990; Meeske. 1988b). The industry’s mandate that even entry-level employees should have experience in the field (Basow & Byrne. 1993; Parcells. 1985) has led colleges and universities to help place students in internships. The programs offer students an opportunity to grow in the professional environment, while supplementing what has been learned in the classroom.
While past studies have extensively examined bow broadcasters and journalists view internships, and what those professionals think of the training entry-level employees receive while in school, little is known about how views of the internship experience relate to newsroom hiring practices and career preparation of students. College students may find it difficult to predict what journalists and broadcasters want in the hiring of newsroom employees. This problem also affects journalism and broadcasting faculty who teach and advise students.
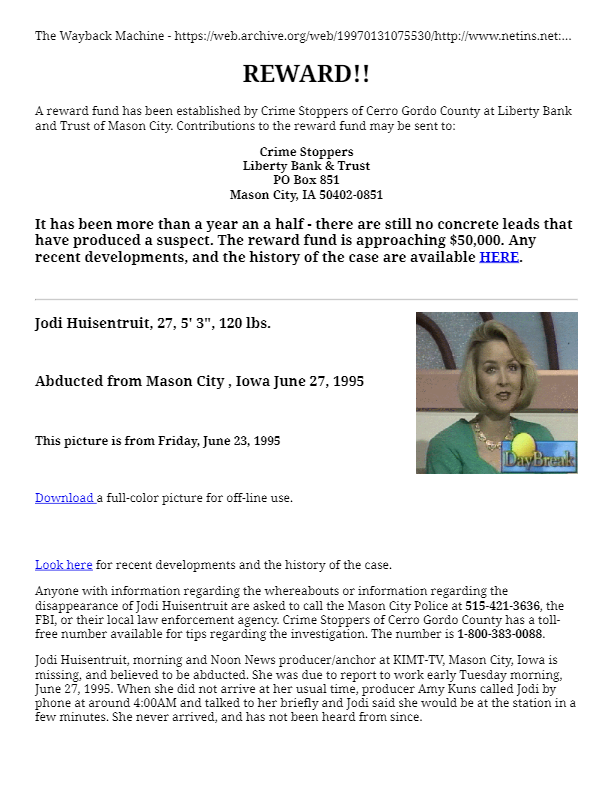
Victims of Abduction: Patterns and Case Studies
INTRODUCTION
In July 1960, eight–year-old Graham Thorne, whose parents had just won the Opera House lottery, was abducted, held for ransom and then murdered by a man known as Stephen Bradley. The case attracted saturation media coverage, in part because, up until that time, cases of abduction and kidnapping were virtually unheard of in Australia. Since 1960, a number of other tragic cases of abduction have also generated widespread public interest and concern. They include the abduction and murder of Anita Cobby, Janine Balding, Samantha Knight and Ebony Simpson.
In 2005, police recorded 393 abductions in New South Wales (NSW). Taken at face value, police figures suggest that NSW has the highest recorded rate of abduction in the country (ABS 2005). Police abduction statistics and medi
Growing Crime: The Rising Use of Fertilizer for Illegal Purposes and the Need for Stricter Regulations Concerning the Sale and Storage
1. lNTRODUCfION
If you pick up a newspaper or turn on the evening news, you would be hard pressed not to find a story about the growing methamphetamine problem in the Midwest.’ In the recent past, stories could be found daily discussing the bombing of the Murrah Federal Building in Oklahoma City,> and the bombing of the’ World Trade Center in New York City.’ Although the problems of methamphetamine (“meth”) and domestic terrorism seem to be unrelated, they share the trait of using a common agricultural tool, fertilizer, to further their growing criminal enterprise.’ This Note will examine the use of fertilizers, particularly anhydrous ammonia and ammonium nitrate, in the illegal production of methamphetamine and explosives.
A Process and Impact Evaluation of the Agricultural Crime, Technology, Information, and Operations Network (ACTION) Program
Abstract
Research Goals and Objectives
Agricultural crime is a serious problem in the United States, with significant financial consequences for farmers, insurers, and consumers—some sources estimate that agricultural crime results in $5 billion in economic losses annually. Yet few prevention or reduction interventions have been developed, and fewer still have been evaluated. As a result, policy makers and practitioners lack critical information about how to deal with this costly problem. The Urban Institute and Florida State University multi-disciplinary research team employed a multi-method approach to evaluate one promising initiative, the Agricultural Crime, Technology, Information, and Operations Network (ACTION) project, located along the southern coast and Central Valley of California and supported by the Bureau of Justice Assistance. The goal of the proposed research was to provide policymakers, practitioners, program developers, and funders with empirically-based information about whether ACTION works. The specific objectives were:
California’s War on Agricultural Crimes – San Joaquin College of Law
INTRODUCTION
Agricultural crime is not the first thing that comes to mind when one thinks about crime in general. Almost all of the information we receive from the media, including crime reports and statistics, is ur ban-based. Little attention is given to rural crime; partly because of the involvement of fewer victims.2 However, the monetary loss and economic damage incurred by these victims is staggering and every bit as damaging to society as urban-based crimes.3 Several factors combine to make farms and ranches easy targets for criminals. First is the isolation of rural areas. Farms generally occupy vast tracts of land, and most are sparsely inhabited
Harrassment Techniques
7.The use of directional speakers which have the ability to direct sound to a single individual in a crowded room. This particular item is ultimately the most used and is often referred to as V2K or Voice to Skull and is used extensively in the psychological breakdown of the victim. The use initially is to cause the victim to doubt their sanity and drive them into the mental health system, and later to just torment and never give the victim a moment of privacy or peace.
Comparing Insider IT Sabotage and Espionage: A Model-Based Analysis
Executive Summary
The purpose of this study is to examine psychological, technical, organizational, and contextual factors we believe contribute to at least two forms of insider trust betrayal: insider sabotage against critical information technology (IT) systems, and espionage. Security professionals and policy leaders currently view espionage and insider threat as serious problems but often as separate issues that should be addressed by a different configuration of security countermeasures. In this study, our team of researchers investigated similarities and differences between insider IT sabotage and espionage cases to assess whether a single analytical framework based on system dynamics modeling could be developed to isolate the major factors or conditions leading to both categories of trust betrayal. Based on the results, it is our position that insider IT sabotage and espionage share many contributing and facilitating system dynamics features. It follows that they might be detected and deterred by the same or similar administrative and technical safeguards. Research into countermeasures that address multiple threats should be of high priority so that organizations can
Street Gangs And Violent Extremist Organizations Learning Across Fields
INTRODUCTION
Street gangs and violent extremist organizations (VEOs) exhibit many similarities: both groups use violence to achieve their objectives, engage in the illicit economy, draw membership from a similar population of marginalized youth, and rely on personal connections for recruitment. Parallels suggest significant potential for cross-disciplinary learning. Yet the groups differ in notable ways, including their goals, targets of violence, relationship to political actors and geographic focus. In terms of membership, key differences include the relevance of family instability, early aggressive behavior and insecure neighborhoods, which are important influences on gang involvement but less important for VEO involvement. At the same time, political drivers and an increase in religiosity are important for VEO involvement but not gang involvement, and there is a broader range of risk factors for and profiles of people involved in VEOs. This paper aims to identify applicable lessons and programming recommendations that can be translated across the two domains. Understanding where street gang and VEO characteristics converge and diverge is important in order to apply learning cogently from one field to the other.
The “Big Picture” of Insider IT Sabotage Across U.S. Critical Infrastructures
Abstract
A study conducted by the U.S. Secret Service and the Carnegie Mellon University Software Engineering Institute CERT Program analyzed 150 insider cyber crimes across U.S. critical infrastructure sectors. Follow-up work by CERT involved detailed group modeling and analysis of 30 cases of insider IT sabotage out of the 150 total cases. Insider IT sabotage includes incidents in which the insider’s primary goal is to sabotagesome aspect of the organization or direct specific harm toward an individual. This paper describes seven general observations about insider IT sabotage based on our empirical data and study findings. We describe a system dynamics model of the insider IT sabotage problem that elaborates complex interactions in the domain and unintended consequences of organizational policies, practices, technology, and culture on insider behavior. We describe the structure of an education and awareness workshop on insider IT sabotage that incorporates the previously mentioned artifacts as well as an interactive instructional case.
Are Suicide Terrorists Suicidal? A Critical Assessment of the Evidence
ABSTRACT
Objective: Most of the research on suicide terrorism is conducted in the political science and international relations fields. The prevailing wisdom within this literature is that suicide terrorists are not suicidal. But how good is the evidence for this assumption? Knowing whether suicide terrorists are suicidal has implications for prevention, rehabilitation, and the “softer” side of counterterrorism designed to win minds and hearts. In addition it may deepen our understanding of suicide itself.
Design: This article uses a review of existing literature to examine the arguments and evidence for and against the possibility that suicide terrorists could be suicidal in the context of a broad range of explanations for suicide terrorism.
Results: Much of the evidence against the possibility that suicide terrorists are suicidal is based on anecdote or faulty assumptions about suicide. Relatively few formal systematic studies of suicidality in suicide terrorists have been conducted. Nonetheless, there is emerging evidence that suicidality may play a role in a significant number of cases.
Developments In The Law Of Vertical Restraints: 2012
I. Standards
A. Are Vertical Resale Price Restraints Still Illegal?
As a result of two U.S. Supreme Court decisions handed down only during the last 15 years, the legality of vertical restraints on maximum and minimum levels of resale prices known otherwise as resale price maintenance (RPM) —under Section 1 of the Sherman Act is now analyzed under the rule of reason. Specifically, in State Oil Co. v. Khan and Leegin Creative Leather Products, Inc. v. PSKS, Inc. , the Court held that both vertical maximum RPM and vertical minimum RPM, respectively, are to be given rule-of-reason treatment. Thus, instead of being summarily condemned as per se illegal, business methods and practices involving the use of vertical maximum or minimum RPM are subjected to an individualized factual inquiry into the nature, purpose and history of those restraints, and their actual or likely effect on competition, in accordance with Justice Brandeis’s classic and enduring formulation in Chicago Board of Trade v. United States. Khan and Leegin have thus brought the antitrust analysis of…
Railroad Dispatcher Communications Training Materials
Background
By law, the Federal Railroad Administration (FRA) has the responsibility of ensuring railroad safety throughout the country. The U.S. rail system includes almost 300,000 miles of track, 20,000 locomotives, 1.2 million freight cars, 6,500 passenger cars, and over 250,000 employees. In an effort to improve safety standards industry-wide, the FRA has adopted a zero-tolerance policy for accidents, injuries, or deaths on the nation’s rails.
Although highway-rail grade crossings and poor track roadbed are implicated in the vast majority of accidents that result in fatalities, the National Transportation Safety Board (NTSB) has determined that dispatcher error has been the probable cause of a number of accidents. Dispatchers are responsible for the safe and timely movement of track occupants through a specified territory. Because 85 percent of the U.S. rail system is “dark territory” (unsignalized track), clear and precise communication between dispatcher and track occupant is essential. Dispatchers are also responsible for the safety of railroad employees working on the track, the management of train crews, and equipment utilization.
An Introduction to Computer-Assisted Train Dispatch
Introduction
Train dispatchers on a centralized traffic controlled (CTC) line control the movement of trains over a line, including the planning of where meets and overtakes are to occur and the aligning of the switches to control each train movement. Increasingly, computers are being used to assist the dispatchers in performing this critical function. This paper is an introduction to the topic of computer-assisted dispatch, and will provide both a framework for judging the progress that has been made and an outline of the research that remains to be done in this area. Centralized traffic control has been in use for over fifty years, the first system being installed in 1927 on the New York Central Railroad. This system permitted a single dispatcher to control the operation of trains in a territory without the use of train orders (detailing to the train engineer before the start of his run exactly where each meet is to take place). Immediate benefits from CTC were the increased…
Time-Space Analysis of Terrorist Planning Cycles
Abstract
Terrorism is among the largest threats to national and international security in today’s global community. Acts of terrorism have resulted economic and societal impacts throughout the world. Improvements in technology have increased the capacity of terrorists to maximize the impact of their actions. The increasing influence and prevalence of terrorist activity has demanded research focused on the prevention of terrorist acts. A known method of terrorism prevention is uncovering a plot during its planning and preparation phase. Terrorist planning can be evaluated based on how actors move through space and time prior to the execution of their attack. General patterns and insights into terrorist planning activities can offer the intelligence, defense, and law enforcement communities with information on how where terrorists can be located in relationship to their target throughout their planning cycle. This movement within a planning cycle can be easily visualized and analyzed through the use of a Time-Space Signature. This research assesses the movements of actors involved in past terrorist activities in…